
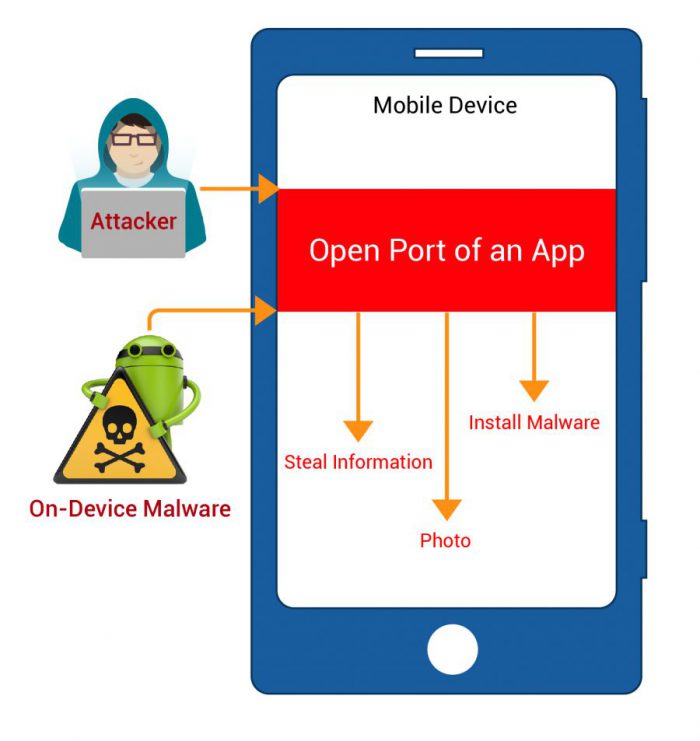
According to research, most of the Android apps have become vulnerable to attackers. Researchers at The University of Michigan stated that there are many applications on PlayStore that can be exploited by hackers, steal user data and even execute malicious code on one’s Mobile. This is applicable for all the apps that have open ports and are not properly managed due to lack of security provided by developers.
“An open port (or a listening port) is a communication endpoint for accepting incoming connections in computer networking model, normally utilized by server applications to deal with demands from remote clients. As the Smartphones are immensely used these days, open port direct exposer can cause severe damaged to end users.
“From the identified vulnerable usage, we discover 410 vulnerable applications with 956 potential exploits in total. We manually confirmed the vulnerabilities for 57 applications, including popular ones with 10 to 50 million downloads on the official market, and also an app that is pre-installed on some device models.” as per the research paper.
These vulnerabilities exploitation can cause immense damaged such as stealing data, information, contacts, photos and security credentials. Further, it can run malicious code and perform malware installation on devices. The most widely recognized issue is identified with the applications like Wi-Fi File Transfer, which enable clients to interface with a port on their cell phone by means of Wi-Fi keeping in mind the end goal to exchange records from a cell phone to a PC. Applications like Wi-Fi File Transfer require attackers to share the same network as the target, this means that only users accessing a public Wi-Fi network or a compromised private network are at risk.
The best way to protect mobile devices from attack is to keep mobile safe with Antivirus products and if required, uninstall those mobile apps that open insecure ports. Alternatively, you can protect these applications by scanning the mobile on regular basis.
Precautions to be taken by User:-
- Keep your software up to date and stop downloading apps from unfamiliar sites.
- Try to avoid free Wi-Fi Connections.
- Keep a tab on the permissions requested by the apps
- Install a reliable mobile security app like REVE mobile security antivirus for complete protection
- RaaS : The Dark Side of SaaS
- Hackers Target MOVEit Transfer’s Zero-Day Vulnerability, Emergency Patch Deployed
- How Scammers Are Utilizing ChatGPT? Few Tips To Be Safe
- World Backup Day: Why Data Backups are Important in Cybersecurity
- What is Social Engineering and How Cyber Criminals Use It
- Things To Know About Personally Identifiable Information (PII)
- What is Data Breach? Why and How It occurs? How To Prevent Data Breach


