Imagine a sailor, a veteran one. His King ordered him to sail through the breathtakingly beautiful Caribbean sea and he was just doing that. With the mesmerizing view all around he got carried away just a bit and suddenly there’s chaos in the deck. The pirates have attacked the ship and there’s no way of avoiding them now, within moments they have made the sailor hostage. In the middle of nowhere, far away from home, the only way left for him is to pay the ransom demanded by the pirates of the Caribbean!
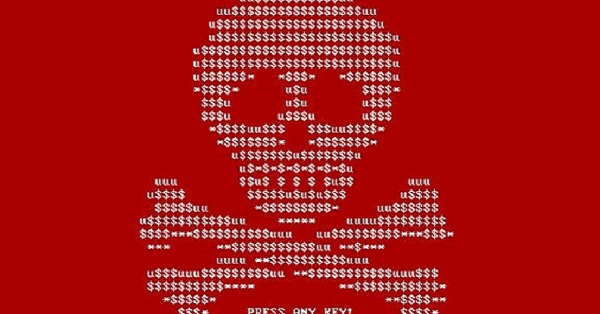
Let’s fast forward the scenario a few hundred years, the year 2020, the year of a new pandemic, and the beginning of mass work from home schedules. You are among those who are leading a team to its goal now. The ship is replaced by the team you lead, and the master instrument to control your ship, the helm, is replaced by your pc. On a fine morning, you see some irregularities with your computer, you try to address the problem and BOOM! A message like the one below pops out!
It’s the pirates, with pernicious effects in a digital form. As they aim the same thing, force you to pay a ransom, by infecting your computer with some kind of a virus, a ransom demanding malware, or simply put Ransomware!
Ransomware is designed in such a way that it blocks user access to files or entire systems by encrypting them. The way to access the encrypted data is to use a decryption key only known to the attacker who demands a ransom to provide it, hence the name ransomware.
If not approached cautiously Ransomware can wreak havoc across organizations as well as personal computers. This article is dedicated to some instantaneous actions which can mitigate ransomware attack loss.
How does Ransomware work?

A Ransomware gets entry via a phishing email or a malicious website. Clicking a link in an email like that or visiting a similar website is enough to permit that malware’s entry into a machine. Even though there are other ways, these two are most common. The attack typically starts at a single workstation and makes its way to all connected machines. This first workstation getting infected has a technical name as the Endpoint.
What’s more alarming is, even if a ransomware gets its way into the endpoint, often it goes undetected. It simply runs its course in the background, searches for new targets to encrypt including other files, workstations, even backups! Only when it gets hold of enough important files, it announces its presence by locking the data and demanding ransoms. Present days, the attackers want the ransom to be paid in cryptocurrencies like Bitcoin so that you can never trace the destination of the ransom you paid. They often mention a deadline for the payment and threaten to destroy or permanently lock the encrypted files forever if the money is not paid in due time!
Is There Any Alternative?

As mentioned earlier, you should never consider paying the ransom right away. Chances are the hackers will simply take your money and never provides you with an encryption key! You might start looking at whether any free decryption tool is available or not. In some events, free decryption keys are made available from law enforcement agencies.
However, there is an old saying –Prevention is better than cure. You need not to go through all these tiresome moments and difficult times if somehow the ransomware’s entry is restricted in the first place. That’s where any antivirus or anti-malware software comes into play. The Reve Antivirus stood tall among others with reviews and recommendations from its users. You can always go and try their 1-month free trial to check if it impresses you or not! Either way, we hope you keep your machine safe from any ransomware attack. In the unfortunate event of an attack, these tips will help you to mitigate ransomware attack loss.
- RaaS : The Dark Side of SaaS
- Hackers Target MOVEit Transfer’s Zero-Day Vulnerability, Emergency Patch Deployed
- How Scammers Are Utilizing ChatGPT? Few Tips To Be Safe
- World Backup Day: Why Data Backups are Important in Cybersecurity
- What is Social Engineering and How Cyber Criminals Use It
- Things To Know About Personally Identifiable Information (PII)
- What is Data Breach? Why and How It occurs? How To Prevent Data Breach


